Imran Shafique Ansari
Enhancing Physical Layer Security in IoT-Based RF-FSO Integrated Networks: Multi-RIS Structures and their Impact on Secure Communication
Sep 18, 2025Abstract:Due to their ability to dynamically control the propagation environment, reconfigurable intelligent surfaces (RISs) offer a promising solution to address the challenges of $6$G wireless communication, especially in the context of Internet of Things (IoT) networks. This paper investigates a mixed communication model with multi-RIS-aided radio frequency (RF)-free space optics (FSO) to enhance the performance of IoT applications in complex environments. An eavesdropper is assumed to be present, attempting to intercept confidential information transmitted over the RF link. All RF links are modeled using Rician fading, while the FSO link accounts for M\'alaga turbulence with pointing errors, capturing real-world propagation conditions. Closed-form analytical expressions are derived for the secrecy outage probability, average secrecy capacity, and effective secrecy throughput in terms of Meijer's G function. To gain further insight, high signal-to-noise approximations of these metrics are also presented. Numerical results highlight the importance of heterodyne detection in mitigating the adverse effects of pointing errors on the FSO link. Moreover, integrating a multi-RIS structure into the proposed model significantly increases secrecy performance, achieving up to a $47.67\%$ improvement in SOP compared to conventional methods. Finally, the derived analytical results are validated through Monte Carlo simulations.
RIS-Aided Free-Space Optics Communications in A2G Networks over Inverted Gamma-Gamma Turbulent Channels
Aug 12, 2024Abstract:With the advent of sixth-generation networks, reconfigurable intelligent surfaces (RISs) have revolutionized wireless communications through dynamic electromagnetic wave manipulation, thereby facilitating the adaptability and unparalleled control of real-time performance evaluations. This study proposed a framework to analyze the performance of RIS-assisted free-space optics (FSO) communication over doubly inverted Gamma-Gamma (IGGG) distributions with pointing error impairments. Furthermore, a special scenario addressing secure communication in the potential presence of an eavesdropper. Consequently, we derived closed-form expressions for the outage probability, average bit error rate, average channel capacity, average secrecy capacity, and secrecy outage probability by employing an asymptotic analysis to provide deeper insights into the influence of various system parameters. Finally, we verified our analytical results through appropriate numerical simulations.
Secrecy Performance Analysis of Integrated RF-UWOC IoT Networks Enabled by UAV and Underwater-RIS
Jul 26, 2024Abstract:In the sixth-generation (6G) Internet of Things (IoT) networks, the use of UAV-mounted base stations and reconfigurable intelligent surfaces (RIS) has been considered to enhance coverage, flexibility, and security in non-terrestrial networks (NTNs). In addition to aerial networks enabled by NTN technologies, the integration of underwater networks with 6G IoT can be considered one of the most innovative challenges in future IoT. Along with such trends in IoT, this study investigates the secrecy performance of IoT networks that integrate radio frequency (RF) UAV-based NTNs and underwater optical wireless communication (UOWC) links with an RIS. Considering three potential eavesdropping scenarios (RF signal, UOWC signal, and both), we derive closed-form expressions for secrecy performance metrics, including average secrecy capacity, secrecy outage probability, probability of strictly positive secrecy capacity, and effective secrecy throughput. Extensive numerical analyses and Monte Carlo simulations elucidate the impact of system parameters such as fading severity, the number of RIS reflecting elements, underwater turbulence, pointing errors, and detection techniques on system security. The findings offer comprehensive design guidelines for developing such a network aiming to enhance secrecy performance and ensure secure communication in diverse and challenging environments.
Trajectory and power design for aerial CRNs with colluding eavesdroppers
Oct 21, 2023



Abstract:Unmanned aerial vehicles (UAVs) can provide wireless access services to terrestrial users without geographical limitations and will become an essential part of the future communication system. However, the openness of wireless channels and the mobility of UAVs make the security of UAV-based communication systems particularly challenging. This work investigates the security of aerial cognitive radio networks (CRNs) with multiple uncertainties colluding eavesdroppers. A cognitive aerial base station transmits messages to cognitive terrestrial users using the spectrum resource of the primary users. All secondary terrestrial users and illegitimate receivers jointly decode the received message. The average secrecy rate of the aerial CRNs is maximized by jointly optimizing the UAV's trajectory and transmission power. An iterative algorithm based on block coordinate descent and successive convex approximation is proposed to solve the non-convex mixed-variable optimization problem. Numerical results verify the effectiveness of our proposed algorithm and show that our scheme improves the secrecy performance of airborne CRNs.
Trajectory and Power Design for Aerial Multi-User Covert Communications
Oct 21, 2023



Abstract:Unmanned aerial vehicles (UAVs) can provide wireless access to terrestrial users, regardless of geographical constraints, and will be an important part of future communication systems. In this paper, a multi-user downlink dual-UAVs enabled covert communication system was investigated, in which a UAV transmits secure information to ground users in the presence of multiple wardens as well as a friendly jammer UAV transmits artificial jamming signals to fight with the wardens. The scenario of wardens being outfitted with a single antenna is considered, and the detection error probability (DEP) of wardens with finite observations is researched. Then, considering the uncertainty of wardens' location, a robust optimization problem with worst-case covertness constraint is formulated to maximize the average covert rate by jointly optimizing power allocation and trajectory. To cope with the optimization problem, an algorithm based on successive convex approximation methods is proposed. Thereafter, the results are extended to the case where all the wardens are equipped with multiple antennas. After analyzing the DEP in this scenario, a tractable lower bound of the DEP is obtained by utilizing Pinsker's inequality. Subsequently, the non-convex optimization problem was established and efficiently coped by utilizing a similar algorithm as in the single-antenna scenario. Numerical results indicate the effectiveness of our proposed algorithm.
RIS-aided Mixed RF-FSO Wireless Networks: Secrecy Performance Analysis with Simultaneous Eavesdropping
Apr 09, 2023



Abstract:The appearance of sixth-generation networks has resulted in the proposal of several solutions to tackle signal loss. One of these solutions is the utilization of reconfigurable intelligent surfaces (RIS), which can reflect or refract signals as required. This integration offers significant potential to improve the coverage area from the sender to the receiver. In this paper, we present a comprehensive framework for analyzing the secrecy performance of a RIS-aided mixed radio frequency (RF)-free space optics (FSO) system, for the first time. Our study assumes that a secure message is transmitted from a RF transmitter to a FSO receiver through an intermediate relay. The RF link experiences Rician fading while the FSO link experiences M\'alaga distributed turbulence with pointing errors. We examine three scenarios: 1) RF-link eavesdropping, 2) FSO-link eavesdropping, and 3) a simultaneous eavesdropping attack on both RF and FSO links. We evaluate the secrecy performance using analytical expressions to compute secrecy metrics such as the average secrecy capacity, secrecy outage probability, strictly positive secrecy capacity, effective secrecy throughput, and intercept probability. Our results are confirmed via Monte-Carlo simulations and demonstrate that fading parameters, atmospheric turbulence conditions, pointing errors, and detection techniques play a crucial role in enhancing secrecy performance.
Secrecy Outage Analysis of Energy Harvesting Relay-based Mixed UOWC-RF Network with Multiple Eavesdroppers
Feb 20, 2023Abstract:This work deals with the physical layer security performance of a dual-hop underwater optical communication (UOWC)-radio frequency (RF) network under the intruding attempts of multiple eavesdroppers via RF links. The intermediate decode and forward relay node between the underwater source and the destination transforms the optical signal into electrical form and re-transmits it to the destination node with the help of harvested energy by the relay from an integrated power beacon within the system. The source-to-relay link (UOWC) follows a mixture exponential generalized Gamma turbulence with pointing error impairments whereas all the remaining links (RF) undergo $\kappa-\mu$ shadowed fading. With regards to the types of intruders, herein two scenarios are considered, i.e., colluding (\textit{Scenario-I}) and non-colluding (\textit{Scenario-II}) eavesdroppers and the analytical expressions of secure outage probability, probability of strictly positive secrecy capacity, and effective secrecy throughput are derived in closed form for each scenario. Furthermore, the impacts of UOWC and RF channel parameters as well as detection techniques on secrecy capacity are demonstrated, and following this a comparison between the two considered scenarios is demonstrated that reveals the collusion between the eavesdroppers imposes the most harmful threat on secrecy throughput but a better secrecy level can be attained adopting diversity at the destination and power beacon nodes along with heterodyne detection rather than intensity modulation and direct detection technique. Finally, all the derived expressions are corroborated via Monte Carlo simulations.
Outage Analysis of Aerial Semi-Grant-Free NOMA Systems
May 12, 2022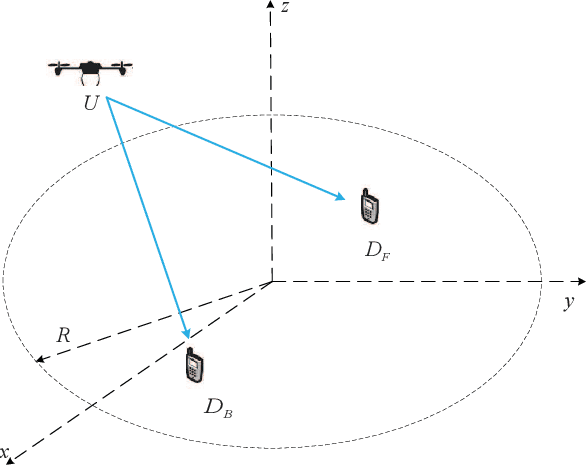
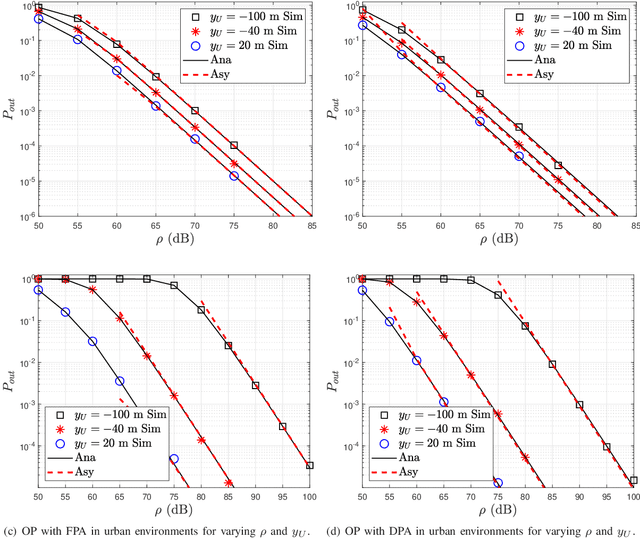
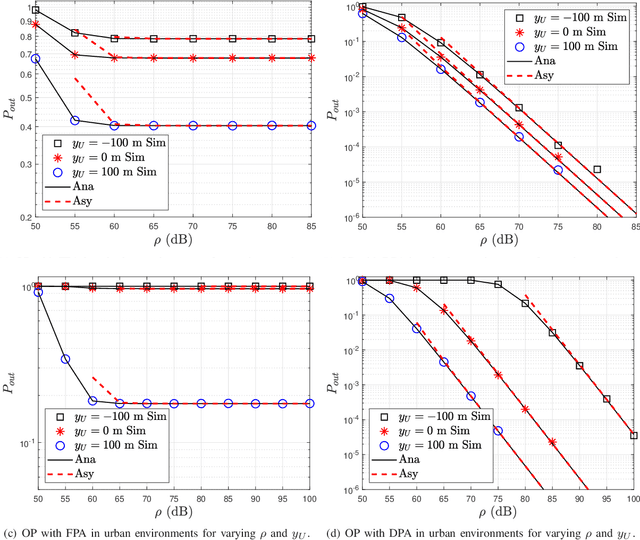
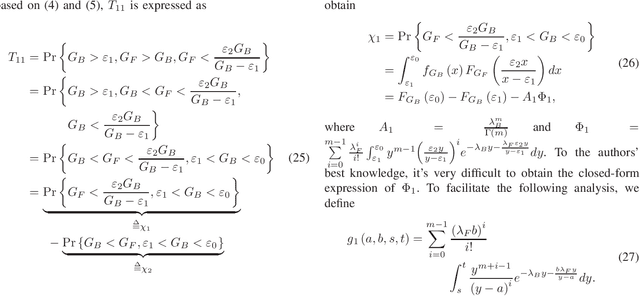
Abstract:In this paper, we analyze the outage performance of unmanned aerial vehicles (UAVs)-enabled downlink non-orthogonal multiple access (NOMA) communication systems with the semi-grant-free (SGF) transmission scheme. A UAV provides coverage services for a grant-based (GB) user and one user is allowed to utilize the same channel resource opportunistically. The hybrid successive interference cancellation scheme is implemented in the downlink NOMA scenarios for the first time. The analytical expressions for the exact and asymptotic outage probability (OP) of the grant-free (GF) user are derived. The results demonstrate that no-zero diversity order can be achieved only under stringent conditions on users' quality of service requirements. Subsequently, we propose an efficient dynamic power allocation (DPA) scheme to relax such data rate constraints to address this issue. The analytical expressions for the exact and asymptotic OP of the GF user with the DPA scheme are derived. Finally, Monte Carlo simulation results are presented to validate the correctness of the derived analytical expressions and demonstrate the effects of the UAV's location and altitude on the OP of the GF user.
Joint Trajectory Design and User Scheduling of Aerial Cognitive Radio Networks
Apr 21, 2022



Abstract:Unmanned aerial vehicles (UAVs) have been widely employed to enhance the end-to-end performance of wireless communications since the links between UAVs and terrestrial nodes are line-of-sight (LoS) with high probability. However, the broadcast characteristics of signal propagation in LoS links make it vulnerable to being wiretapped by malicious eavesdroppers, which poses a considerable challenge to the security of wireless communications. This paper investigates the security of aerial cognitive radio networks (CRNs). An airborne base station transmits confidential messages to secondary users utilizing the same spectrum as the primary network. An aerial base station transmits jamming signals to suppress the eavesdropper to enhance secrecy performance. The uncertainty of eavesdropping node locations is considered, and the average secrecy rate of the cognitive user is maximized by optimizing multiple users' scheduling, the UAVs' trajectory, and transmit power. To solve the non-convex optimization problem with mixed multiple integers variable problem, we propose an iterative algorithm based on block coordinate descent and successive convex approximation. Numerical results verify the effectiveness of our proposed algorithm and demonstrate that our scheme is beneficial to improving the secrecy performance of aerial CRNs.
On Effective Secrecy Throughput of Underlay Spectrum Sharing $α$-$μ$/ Málaga Hybrid Model under Interference-and-Transmit Power Constraints
Nov 12, 2021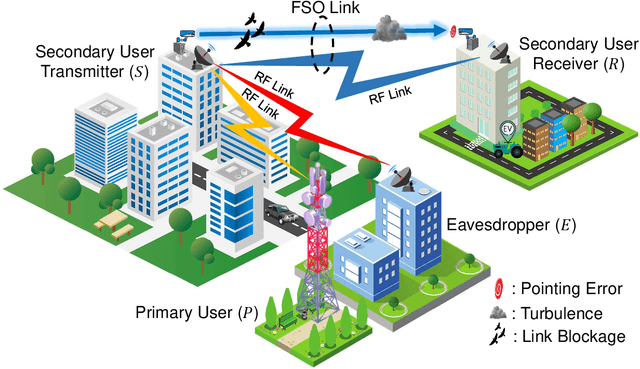
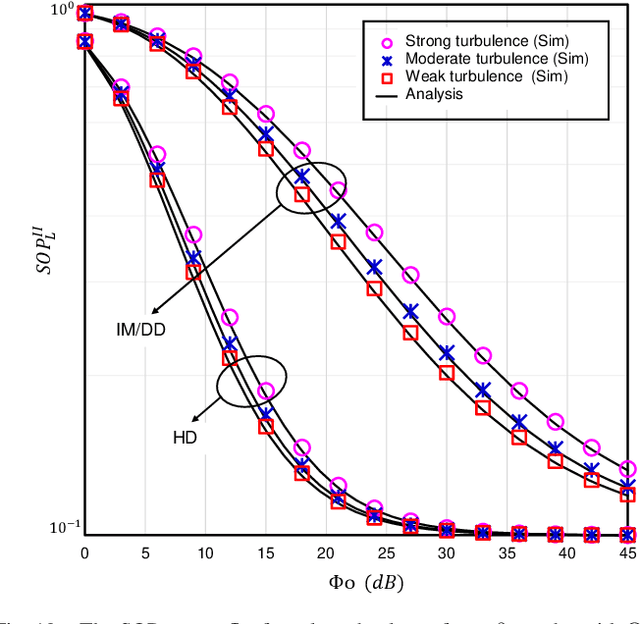
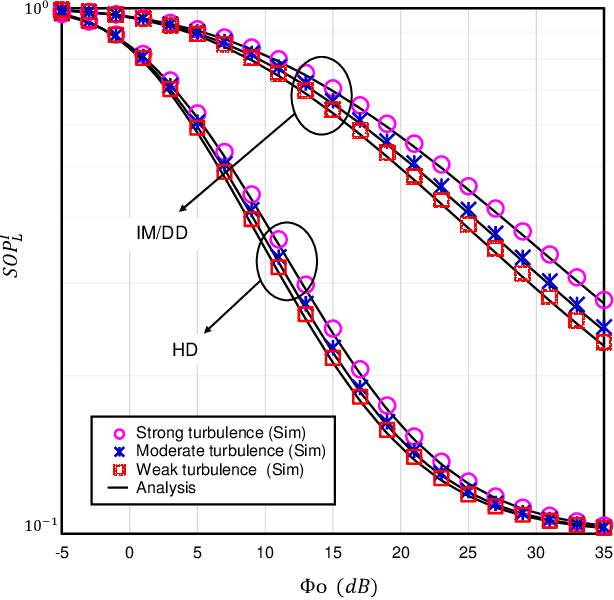
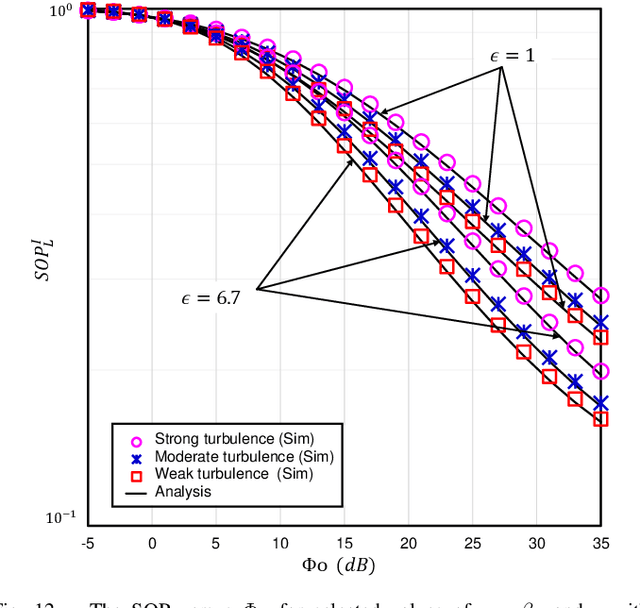
Abstract:The underlay cognitive radio-based hybrid radio frequency / free-space optical (RF / FSO) systems have been emerged as a promising technology due to its ability to eliminate spectrum scarcity and spectrum under-utilization problems. Consequently, this work analyzes the physical layer security aspects of a cognitive RF / FSO hybrid network that includes a primary user, a secondary source, a secondary receiver, and an eavesdropper where the secret communication takes place between two legitimate secondary peers over the RF and FSO links simultaneously, and the eavesdropper can overhear the RF link only. In particular, the maximum transmit power limitation at the secondary user as well as the permissible interference power restriction at the primary user are also taken into consideration. All the RF links are modeled with $\alpha$-$\mu$ fading whereas the FSO link undergoes M\'alaga (M) turbulence with link blockage and pointing error impairments. At the receiver, the selection combining diversity technique is utilized to select the signal with the best electrical signal-to-ratio (SNR). Moreover, the closed-form expressions for the secrecy outage probability, probability of strictly positive secrecy capacity, and effective secrecy throughput are derived to analyze the secrecy performance. Besides, the impacts of fading, primary-secondary interference, detection techniques, link blockage probability, atmospheric turbulence, and pointing error are examined. Finally, Monte-Carlo simulations are performed to corroborate the derived expressions.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge