Andreas Weinand
Towards Energy Impact on AI-Powered 6G IoT Networks: Centralized vs. Decentralized
Apr 21, 2026Abstract:The emergence of sixth-generation (6G) technologies has introduced new challenges and opportunities for machine learning (ML) applications in Internet of Things (IoT) networks, particularly concerning energy efficiency. As model training and data transmission contribute significantly to energy consumption, optimizing these processes has become critical for sustainable system design. This study first conduct analysis on the energy consumption model for both centralized and decentralized architecture and then presents a testbed deployed within the German railway infrastructure, leveraging sensor data for ML-based predictive maintenance. A comparative analysis of distributed versus Centralized Learning (CL) architectures reveals that distributed models maintain competitive predictive accuracy (~90%) while reducing overall electricity consumption by up to 70%. These findings underscore the potential of distributed ML to improve energy efficiency in real-world IoT deployments, particularly by mitigating transmission-related energy costs.
Deep Learning-Based Physical Layer Authentication Using 5G NR Sounding Reference Signals: A Temporal Generalization Study on Real Testbed Data
Apr 11, 2026Abstract:Physical Layer Authentication (PLA) exploits the spatial uniqueness of wireless channel characteristics in order to authenticate devices without recourse to higher-layer cryptographic protocols, which remain vulnerable to key compromise. This paper reports a comprehensive PLA system constructed on 5G New Radio (NR) Sounding Reference Signals (SRS) extracted from a real OpenAirInterface (OAI) testbed operating in band n78 (3.5 GHz) with 40 MHz bandwidth and 30 kHz subcarrier spacing. The proposed approach extracts a 2,531-dimensional feature vector per SRS probe, combining per-subcarrier channel state information (1,248 amplitude and 1,247 differential-phase coefficients), power delay profile taps, delay spread, Doppler statistics, and nonlinear dynamics indicators. A deep one-dimensional Residual Network (1D-ResNet) augmented with Squeeze-and-Excitation (SE) attention blocks is employed to classify each probe as either legitimate or spoofed. Evaluation is conducted on 20,317 over-the-air SRS probes acquired across four measurement sessions using a USRP B210 software-defined radio as the legitimate device and a commercial mobile handset as the attacker. Under a strict chronological train/validation/test split that eliminates temporal leakage, an Equal Error Rate (EER) of 3.92% is attained, with AUC = 0.962 on the held-out test set, and an authentication latency of less than 0.1 ms per probe, which is compatible with 5G Ultra-Reliable Low-Latency Communications (URLLC) requirements.
Keep Private Networks Private II: Wideband Secret Key Generation on a Real 5G NR Testbed
Apr 08, 2026Abstract:Secret key generation (SKG) from wireless channel reciprocity has been demonstrated on WiFi, LTE, and LoRaWAN, but has never been demonstrated on 5G New Radio (NR) Sounding Reference Signal (SRS) and CSI Reference Signal (CSIRS) measurements.
Supervised Learning for Physical Layer based Message Authentication in URLLC scenarios
Sep 13, 2019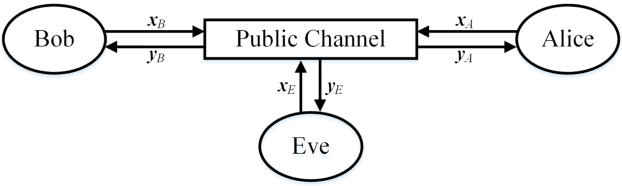
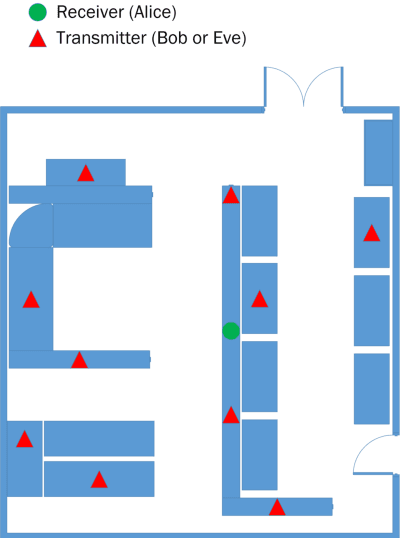
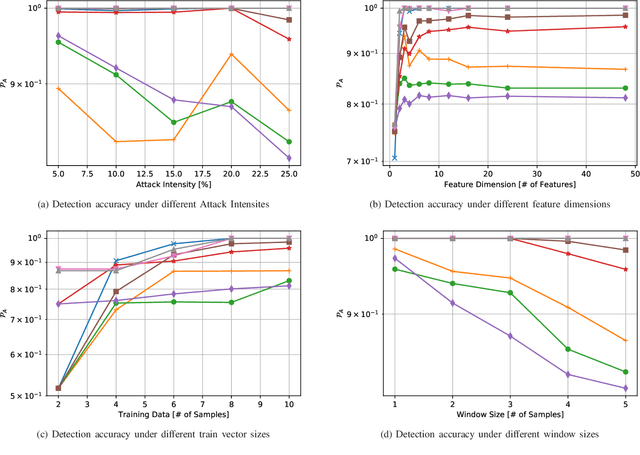
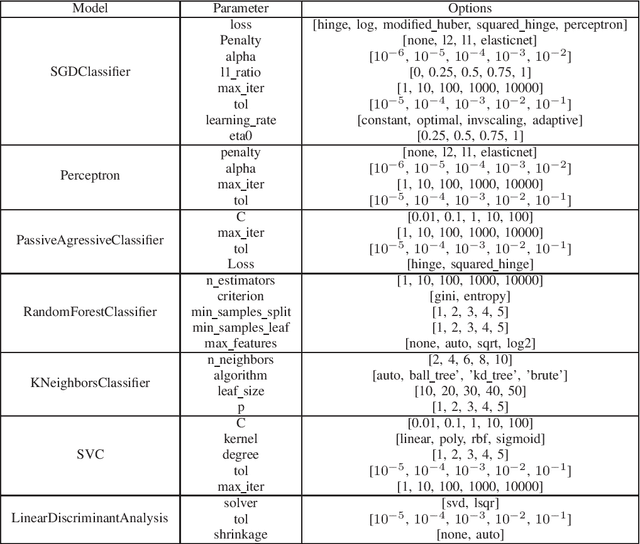
Abstract:PHYSEC based message authentication can, as an alternative to conventional security schemes, be applied within \gls{urllc} scenarios in order to meet the requirement of secure user data transmissions in the sense of authenticity and integrity. In this work, we investigate the performance of supervised learning classifiers for discriminating legitimate transmitters from illegimate ones in such scenarios. We further present our methodology of data collection using \gls{sdr} platforms and the data processing pipeline including e.g. necessary preprocessing steps. Finally, the performance of the considered supervised learning schemes under different side conditions is presented.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge