Naima Kaabouch
Phishing Attacks Detection -- A Machine Learning-Based Approach
Jan 26, 2022Abstract:Phishing attacks are one of the most common social engineering attacks targeting users emails to fraudulently steal confidential and sensitive information. They can be used as a part of more massive attacks launched to gain a foothold in corporate or government networks. Over the last decade, a number of anti-phishing techniques have been proposed to detect and mitigate these attacks. However, they are still inefficient and inaccurate. Thus, there is a great need for efficient and accurate detection techniques to cope with these attacks. In this paper, we proposed a phishing attack detection technique based on machine learning. We collected and analyzed more than 4000 phishing emails targeting the email service of the University of North Dakota. We modeled these attacks by selecting 10 relevant features and building a large dataset. This dataset was used to train, validate, and test the machine learning algorithms. For performance evaluation, four metrics have been used, namely probability of detection, probability of miss-detection, probability of false alarm, and accuracy. The experimental results show that better detection can be achieved using an artificial neural network.
A Performance Comparison of Data Mining Algorithms Based Intrusion Detection System for Smart Grid
Dec 31, 2019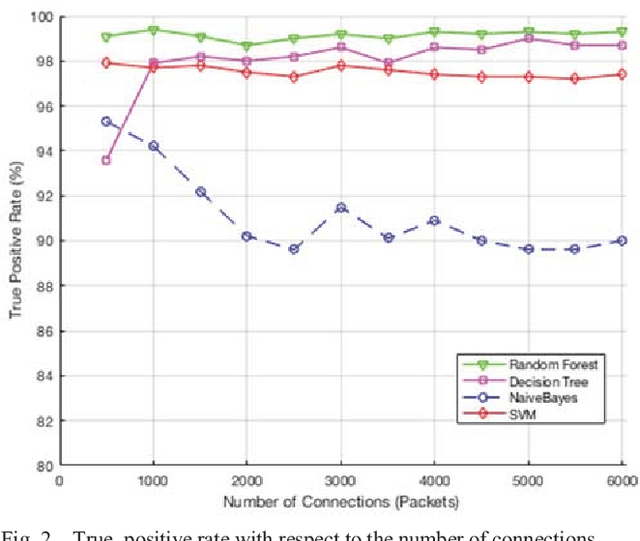
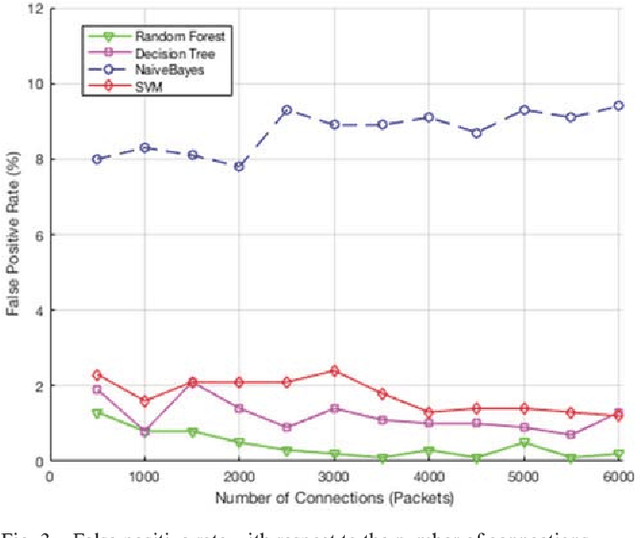
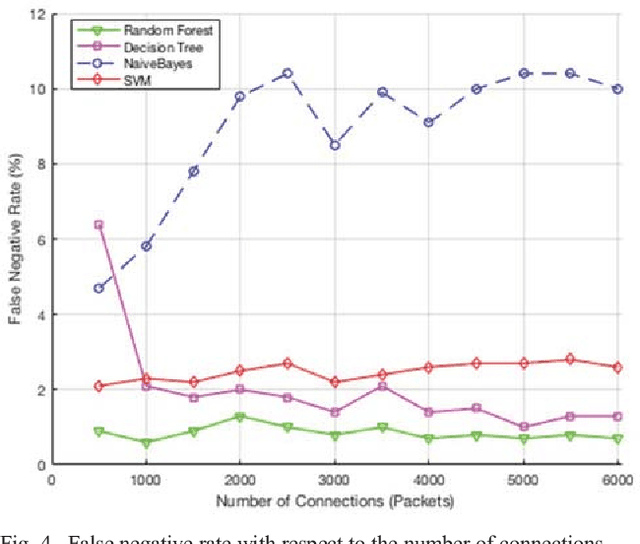
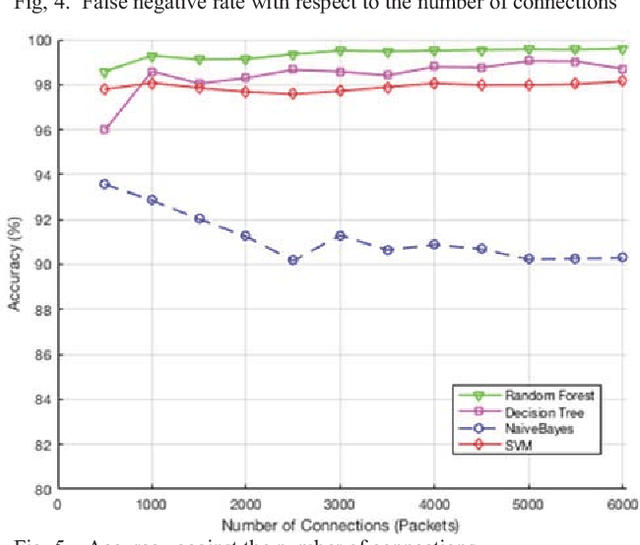
Abstract:Smart grid is an emerging and promising technology. It uses the power of information technologies to deliver intelligently the electrical power to customers, and it allows the integration of the green technology to meet the environmental requirements. Unfortunately, information technologies have its inherent vulnerabilities and weaknesses that expose the smart grid to a wide variety of security risks. The Intrusion detection system (IDS) plays an important role in securing smart grid networks and detecting malicious activity, yet it suffers from several limitations. Many research papers have been published to address these issues using several algorithms and techniques. Therefore, a detailed comparison between these algorithms is needed. This paper presents an overview of four data mining algorithms used by IDS in Smart Grid. An evaluation of performance of these algorithms is conducted based on several metrics including the probability of detection, probability of false alarm, probability of miss detection, efficiency, and processing time. Results show that Random Forest outperforms the other three algorithms in detecting attacks with higher probability of detection, lower probability of false alarm, lower probability of miss detection, and higher accuracy.
* 6 pages, 6 Figures
Primary User Emulation Attacks: A Detection Technique Based on Kalman Filter
Mar 08, 2019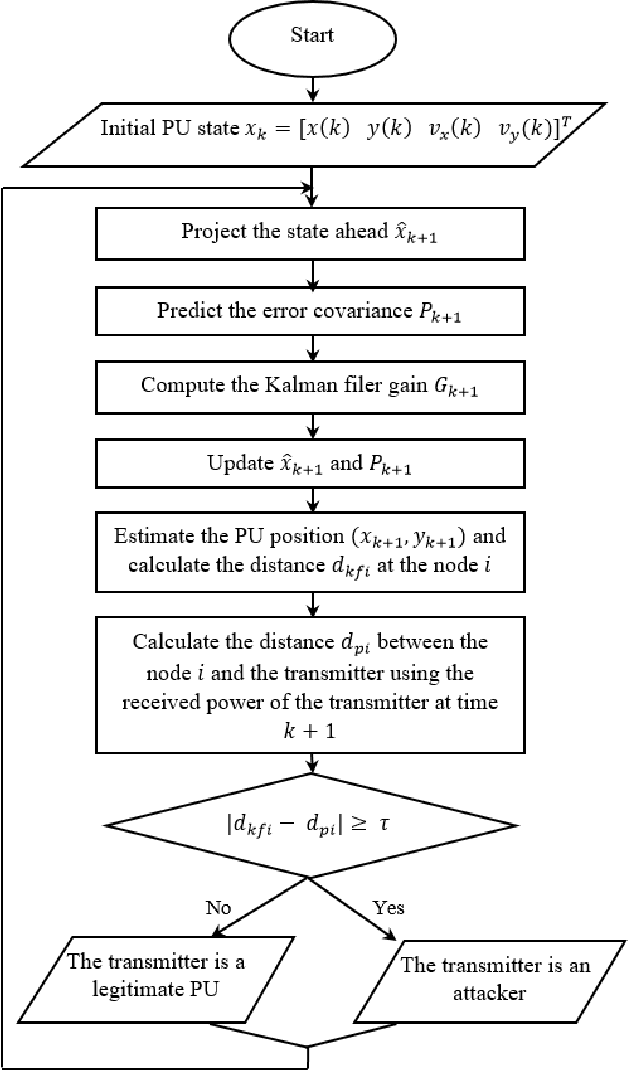
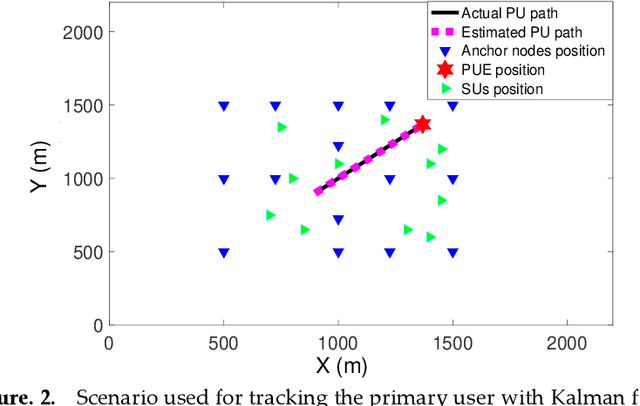
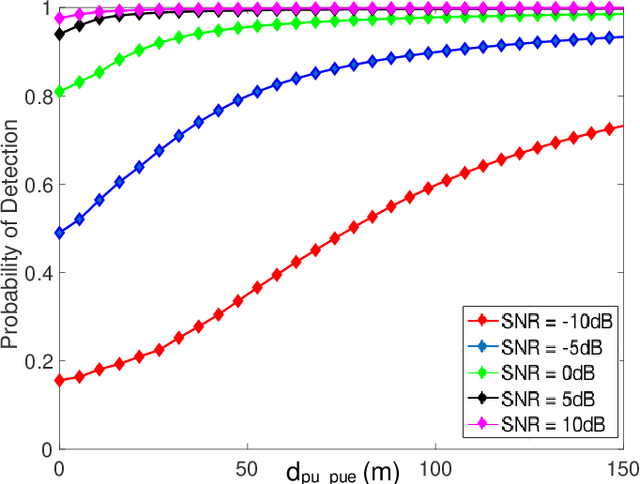
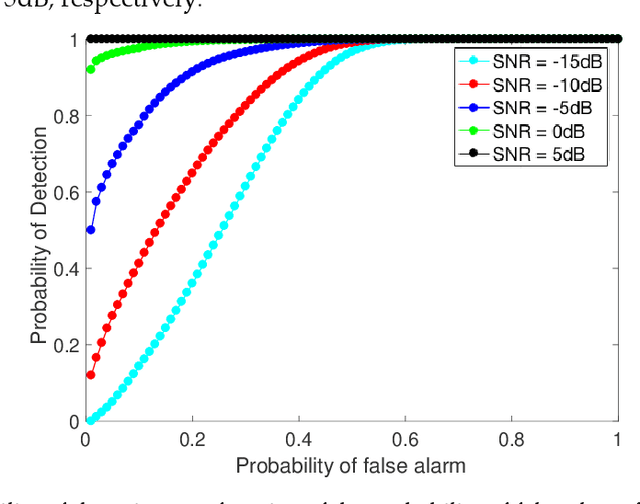
Abstract:Cognitive radio technology addresses the problem of spectrum scarcity by allowing secondary users to use the vacant spectrum bands without causing interference to the primary users. However, several attacks could disturb the normal functioning of the cognitive radio network. Primary user emulation attacks are one of the most severe attacks in which a malicious user emulates the primary user signal characteristics to either prevent other legitimate secondary users from accessing the idle channels or causing harmful interference to the primary users. There are several proposed approaches to detect the primary user emulation attackers. However, most of these techniques assume that the primary user location is fixed, which does not make them valid when the primary user is mobile. In this paper, we propose a new approach based on the Kalman filter framework for detecting the primary user emulation attacks with a non-stationary primary user. Several experiments have been conducted and the advantages of the proposed approach are demonstrated through the simulation results.
* 14 pages, 9 figures
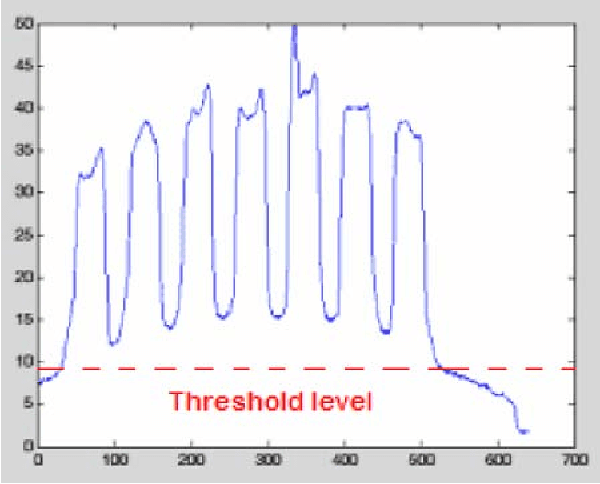
Automatic Techniques for Gridding cDNA Microarray Images
Jul 03, 2016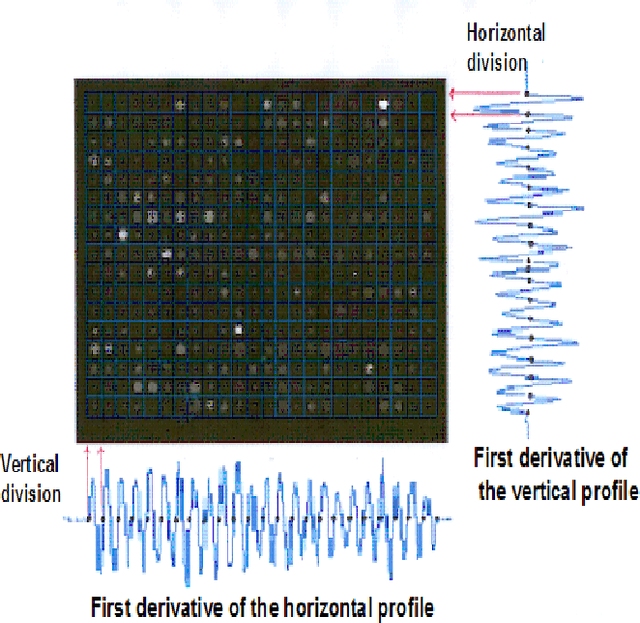
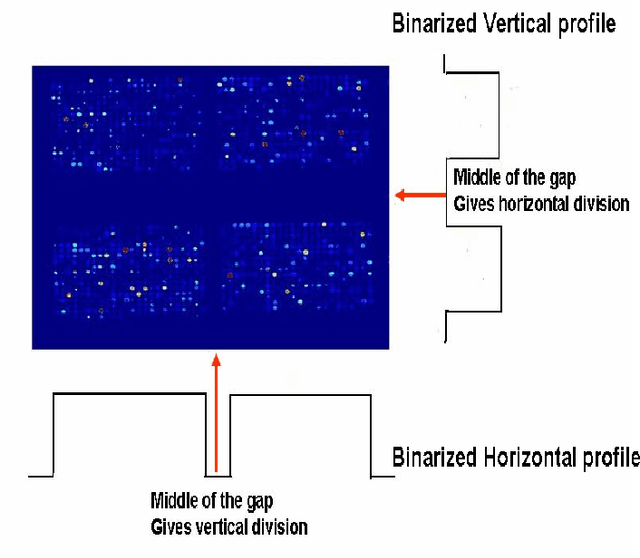
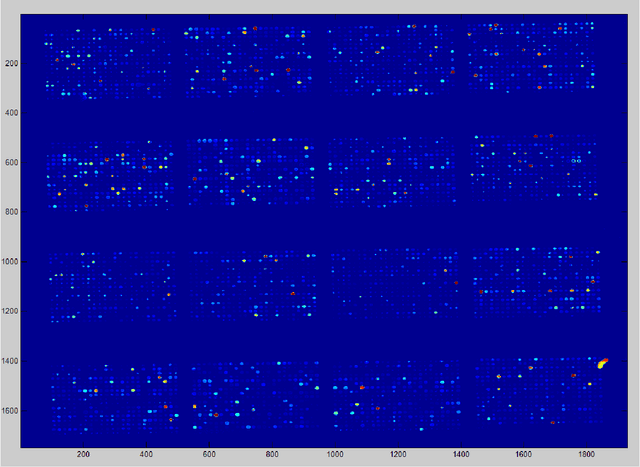
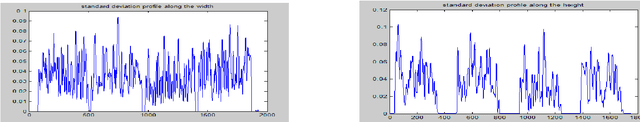
Abstract:Microarray is considered an important instrument and powerful new technology for large-scale gene sequence and gene expression analysis. One of the major challenges of this technique is the image processing phase. The accuracy of this phase has an important impact on the accuracy and effectiveness of the subsequent gene expression and identification analysis. The processing can be organized mainly into four steps: gridding, spot isolation, segmentation, and quantification. Although several commercial software packages are now available, microarray image analysis still requires some intervention by the user, and thus a certain level of image processing expertise. This paper describes and compares four techniques that perform automatic gridding and spot isolation. The proposed techniques are based on template matching technique, standard deviation, sum, and derivative of these profiles. Experimental results show that the accuracy of the derivative of the sum profile is highly accurate compared to other techniques for good and poor quality microarray images.
An Analysis System for DNA Gel Electrophoresis Images Based on Automatic Thresholding an Enhancement
Jul 03, 2016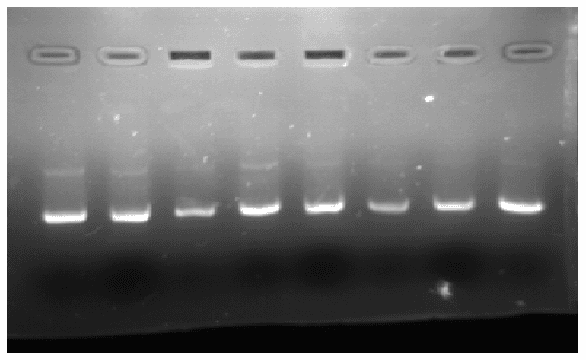
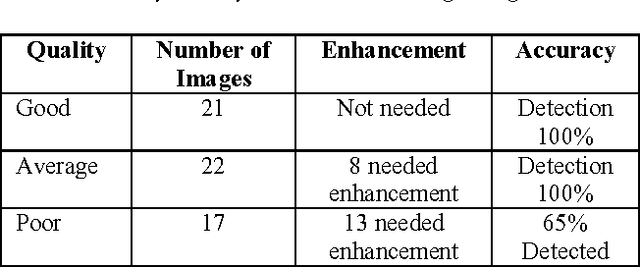
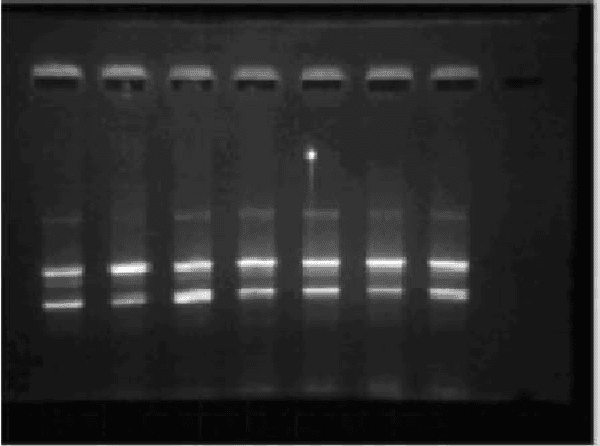
Abstract:Gel electrophoresis, a widely used technique to separate DNA according to their size and weight, generates images that can be analyzed automatically. Manual or semiautomatic image processing presents a bottleneck for further development and leads to reproducibility issues. In this paper, we present a fully automated system with high accuracy for analyzing DNA and proteins. The proposed algorithm consists of four main steps: automatic thresholding, shifting, filtering, and data processing. Automatic thresholding, used to equalize the gray values of the gel electrophoresis image background, is one of the novel operations in this algorithm. Enhancement is also used to improve poor quality images that have faint DNA bands. Experimental results show that the proposed technique eliminates defects due to noise for average quality gel electrophoresis images, while it also improves the quality of poor images.
* 6 pages
Alternative Technique to Asymmetry Analysis-Based Overlapping for Foot Ulcer Examination: Scalable Scanning
Jun 11, 2016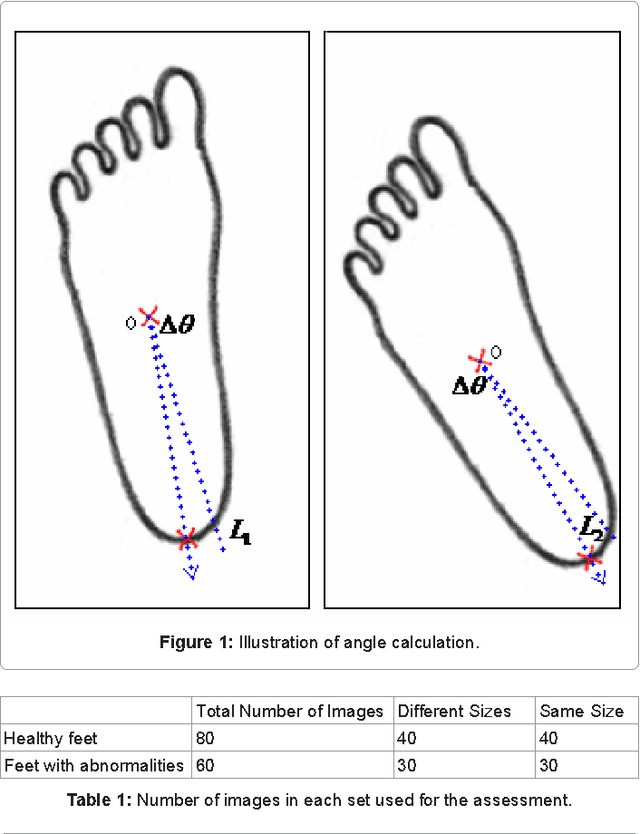
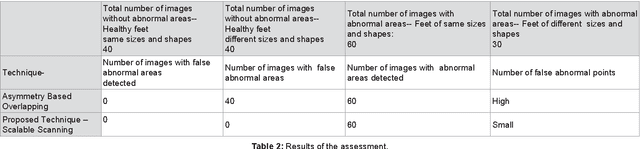
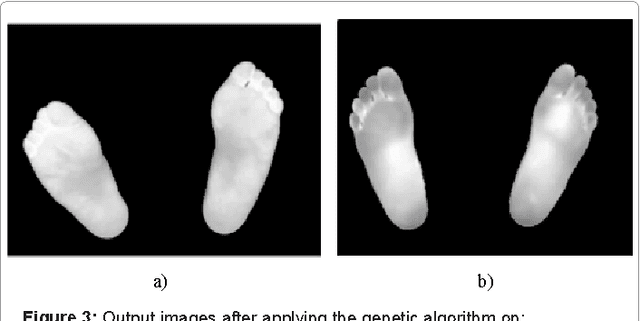
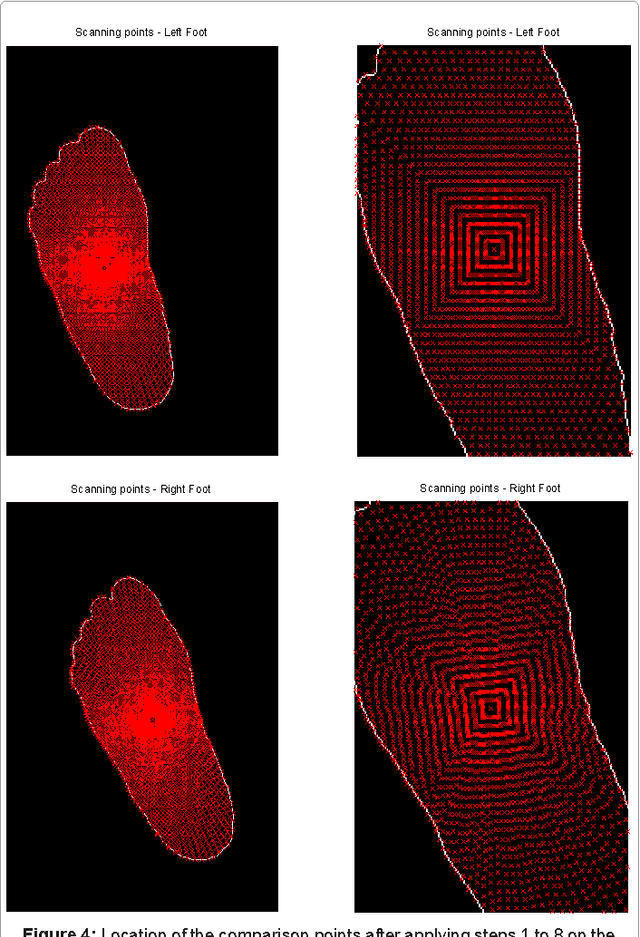
Abstract:Asymmetry analysis based on the overlapping of thermal images proved able to detect inflammation and, predict foot ulceration. This technique involves three main steps: segmentation, geometric transformation, and overlapping. However, the overlapping technique, which consists of subtracting the intensity levels of the right foot from those of the left foot, can also detect false abnormal areas if the projections of the left and right feet are not the same. In this paper, we present an alternative technique to asymmetry analysis-based overlapping. The proposed technique, scalable scanning, allows for an effective comparison even if the shapes and sizes of the feet projections appear differently in the image. The tested results show that asymmetry analysis- based scalable scanning provides fewer false abnormal areas than does asymmetry analysis -based overlapping.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge