Ala Al-Fuqaha
Artificial Intelligence-Assisted Energy and Thermal Comfort Control for Sustainable Buildings: An Extended Representation of the Systematic Review
Jun 22, 2020Abstract:Discussion of the environmental impact of buildings has been gaining weight in the agendas of a number of cities and countries around the world. Indeed, approximately 38% of the final energy consumption growth between 2015 and 2050 in the world is correlated to the use and occupation of buildings. In this regard, the building sector was identified as a leading contributor to global production of CO2 in the fifth report produced by the International Panel of Climate Change (IPCC). However, the same report also has identified this sector as the one with the greatest potential for reducing CO2 emissions through design opportunities, technological advances, and user behavior. Nowadays, research has been directed towards more advanced control structures that take multiple inputs (temperature, humidity, comfort sensation, etc.) and uses artificial intelligence (AI) techniques for heating, ventilation, and air-conditioning (HVAC) control, design, management, optimization, and maintenance. This paper performs a systematic review in order to investigate the use of AI-based tools for improving the performance of energy control systems and enhance thermal comfort. This enables a holistic understanding of (1) the challenges of providing thermal comfort to the users inside buildings in an energy efficient way, and (2) the related bibliographic material to help researchers and professionals in the area undertaking such a challenge. Compared to existing reviews, this paper extends the state of the art by reviewing and categorizing all existing publications and providing the material related to the AI-assisted tools for building environment control while considering a dynamic interaction within comfort-subject-energy control loop.
Deriving Emotions and Sentiments from Visual Content: A Disaster Analysis Use Case
Feb 03, 2020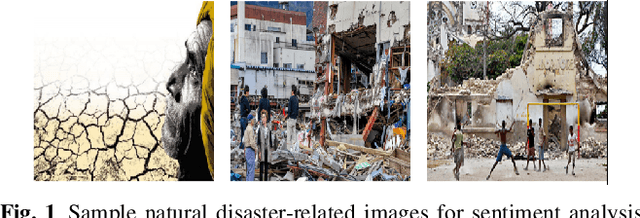
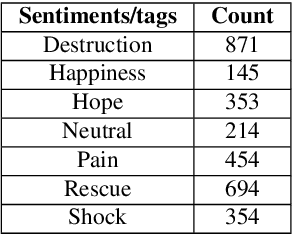
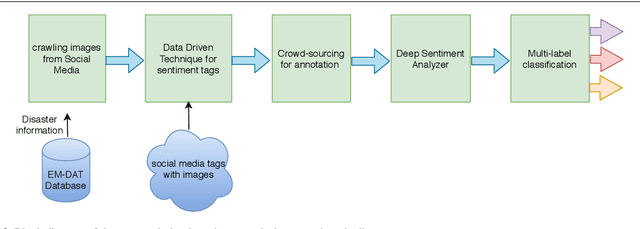
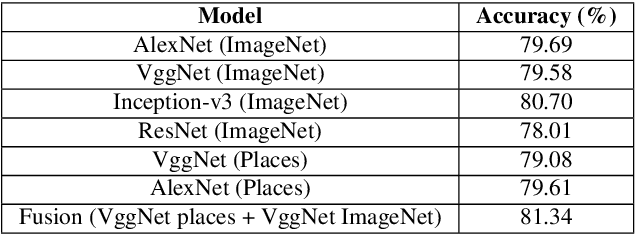
Abstract:Sentiment analysis aims to extract and express a person's perception, opinions and emotions towards an entity, object, product and a service, enabling businesses to obtain feedback from the consumers. The increasing popularity of the social networks and users' tendency towards sharing their feelings, expressions and opinions in text, visual and audio content has opened new opportunities and challenges in sentiment analysis. While sentiment analysis of text streams has been widely explored in the literature, sentiment analysis of images and videos is relatively new. This article introduces visual sentiment analysis and contrasts it with textual sentiment analysis with emphasis on the opportunities and challenges in this nascent research area. We also propose a deep visual sentiment analyzer for disaster-related images as a use-case, covering different aspects of visual sentiment analysis starting from data collection, annotation, model selection, implementation and evaluations. We believe such rigorous analysis will provide a baseline for future research in the domain.
Challenges and Countermeasures for Adversarial Attacks on Deep Reinforcement Learning
Jan 27, 2020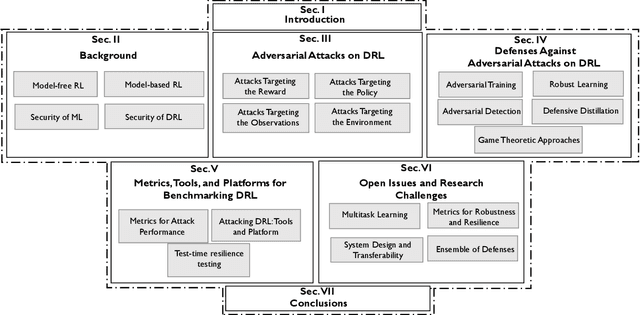
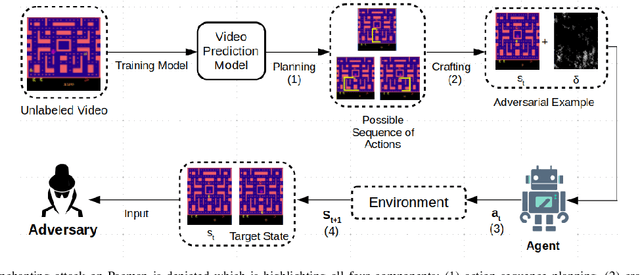
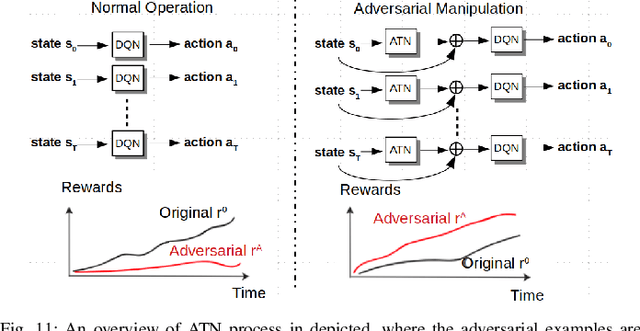
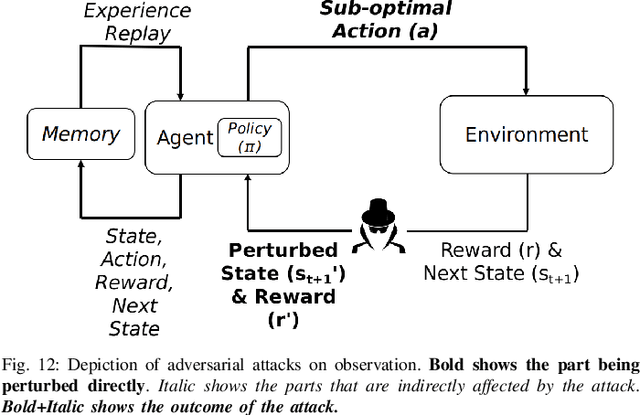
Abstract:Deep Reinforcement Learning (DRL) has numerous applications in the real world thanks to its outstanding ability in quickly adapting to the surrounding environments. Despite its great advantages, DRL is susceptible to adversarial attacks, which precludes its use in real-life critical systems and applications (e.g., smart grids, traffic controls, and autonomous vehicles) unless its vulnerabilities are addressed and mitigated. Thus, this paper provides a comprehensive survey that discusses emerging attacks in DRL-based systems and the potential countermeasures to defend against these attacks. We first cover some fundamental backgrounds about DRL and present emerging adversarial attacks on machine learning techniques. We then investigate more details of the vulnerabilities that the adversary can exploit to attack DRL along with the state-of-the-art countermeasures to prevent such attacks. Finally, we highlight open issues and research challenges for developing solutions to deal with attacks for DRL-based intelligent systems.
Secure and Robust Machine Learning for Healthcare: A Survey
Jan 21, 2020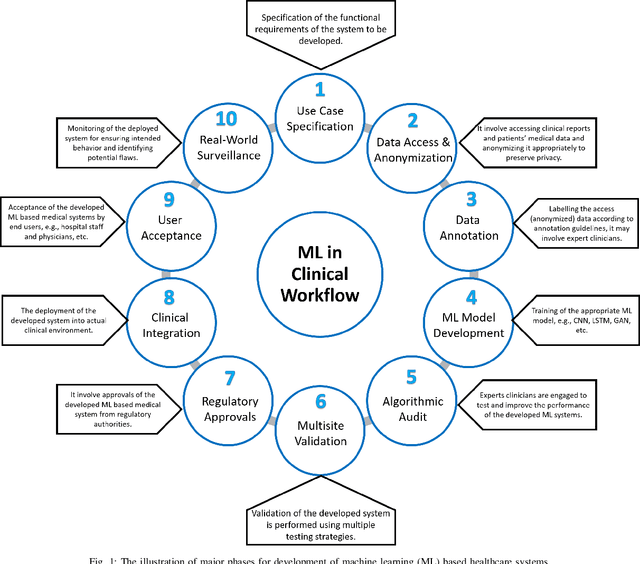
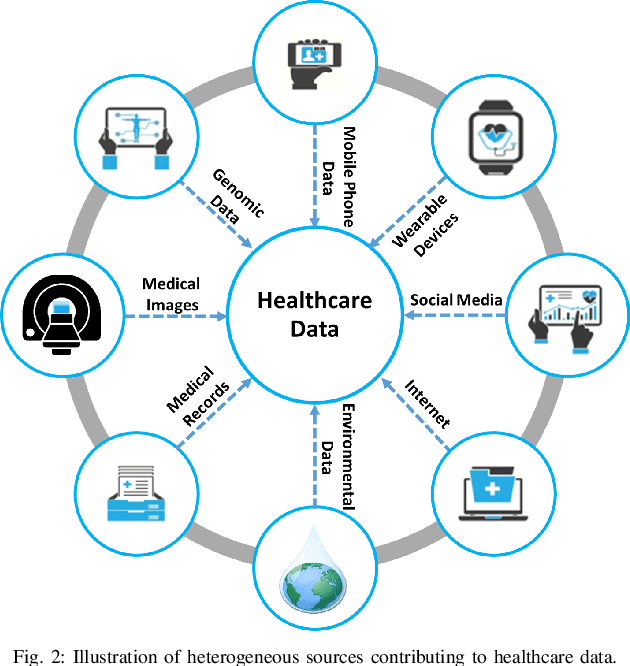
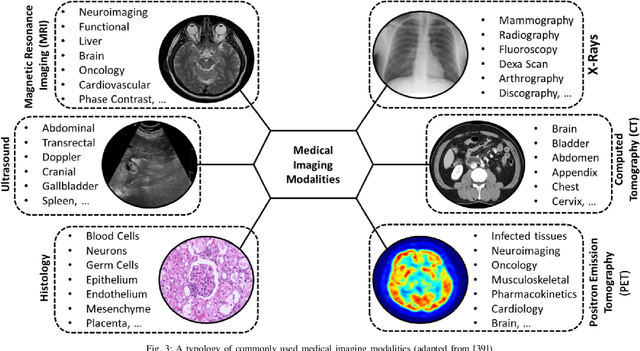
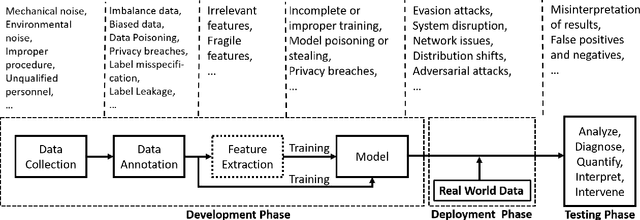
Abstract:Recent years have witnessed widespread adoption of machine learning (ML)/deep learning (DL) techniques due to their superior performance for a variety of healthcare applications ranging from the prediction of cardiac arrest from one-dimensional heart signals to computer-aided diagnosis (CADx) using multi-dimensional medical images. Notwithstanding the impressive performance of ML/DL, there are still lingering doubts regarding the robustness of ML/DL in healthcare settings (which is traditionally considered quite challenging due to the myriad security and privacy issues involved), especially in light of recent results that have shown that ML/DL are vulnerable to adversarial attacks. In this paper, we present an overview of various application areas in healthcare that leverage such techniques from security and privacy point of view and present associated challenges. In addition, we present potential methods to ensure secure and privacy-preserving ML for healthcare applications. Finally, we provide insight into the current research challenges and promising directions for future research.
Exploiting Unlabeled Data in Smart Cities using Federated Learning
Jan 10, 2020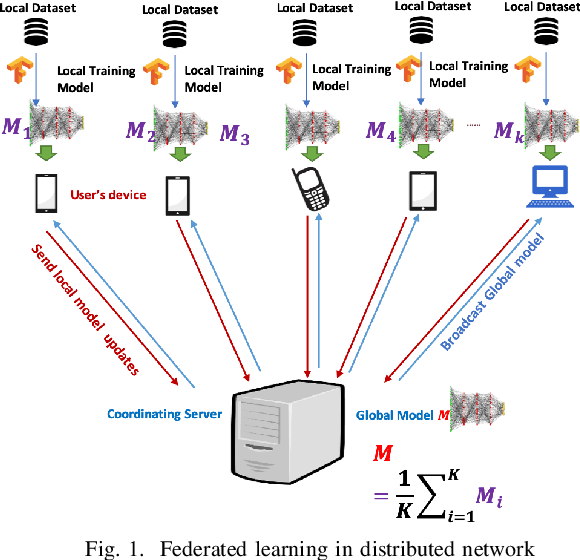
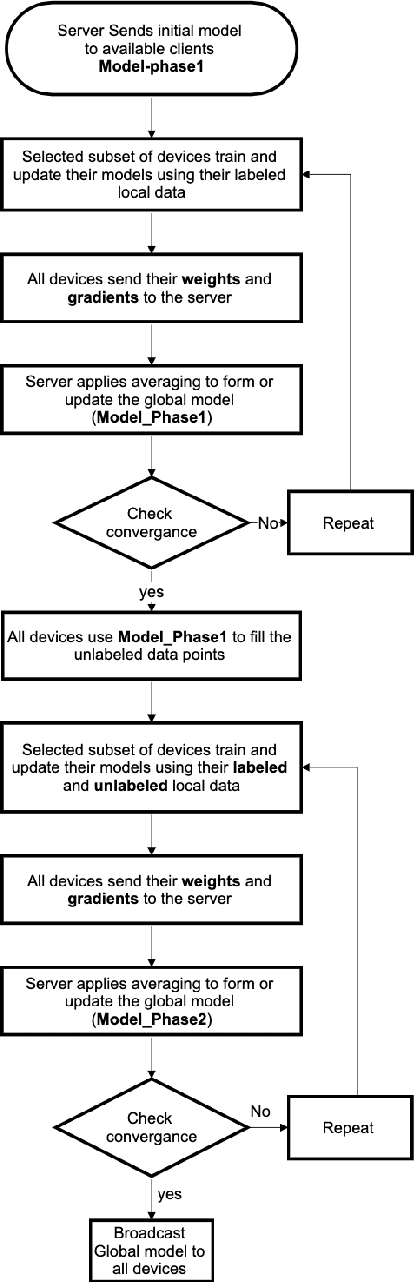
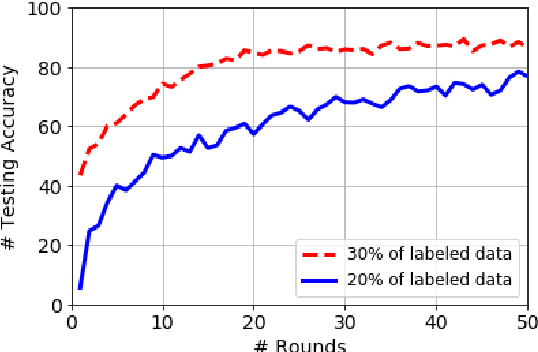
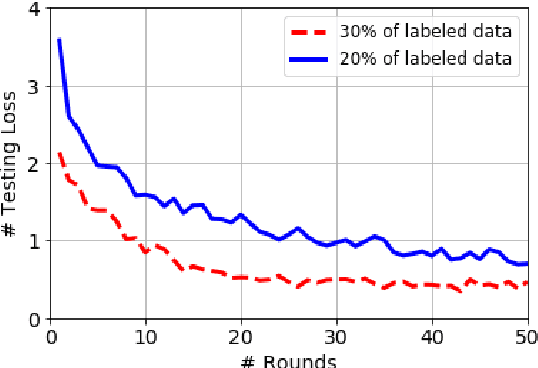
Abstract:Privacy concerns are considered one of the main challenges in smart cities as sharing sensitive data brings threatening problems to people's lives. Federated learning has emerged as an effective technique to avoid privacy infringement as well as increase the utilization of the data. However, there is a scarcity in the amount of labeled data and an abundance of unlabeled data collected in smart cities, hence there is a need to use semi-supervised learning. We propose a semi-supervised federated learning method called FedSem that exploits unlabeled data. The algorithm is divided into two phases where the first phase trains a global model based on the labeled data. In the second phase, we use semi-supervised learning based on the pseudo labeling technique to improve the model. We conducted several experiments using traffic signs dataset to show that FedSem can improve accuracy up to 8% by utilizing the unlabeled data in the learning process.
Sentiment Analysis from Images of Natural Disasters
Oct 10, 2019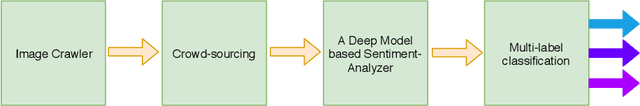
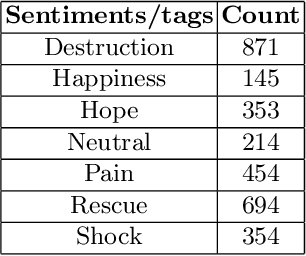
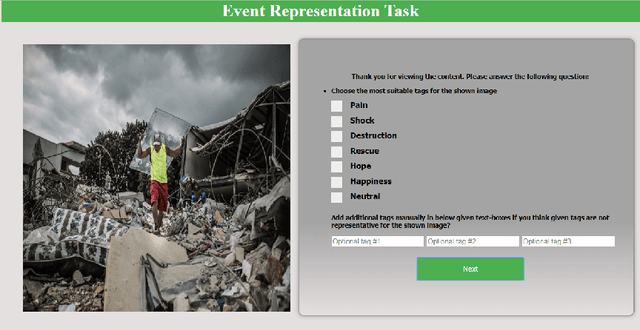
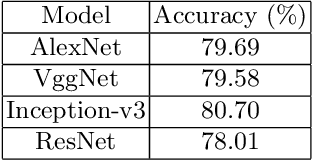
Abstract:Social media have been widely exploited to detect and gather relevant information about opinions and events. However, the relevance of the information is very subjective and rather depends on the application and the end-users. In this article, we tackle a specific facet of social media data processing, namely the sentiment analysis of disaster-related images by considering people's opinions, attitudes, feelings and emotions. We analyze how visual sentiment analysis can improve the results for the end-users/beneficiaries in terms of mining information from social media. We also identify the challenges and related applications, which could help defining a benchmark for future research efforts in visual sentiment analysis.
Multi-Modal Machine Learning for Flood Detection in News, Social Media and Satellite Sequences
Oct 07, 2019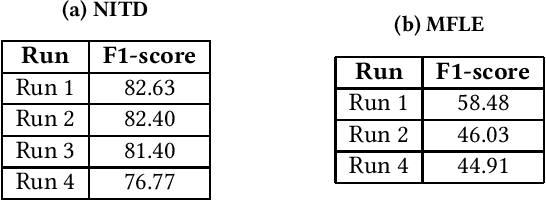
Abstract:In this paper we present our methods for the MediaEval 2019 Mul-timedia Satellite Task, which is aiming to extract complementaryinformation associated with adverse events from Social Media andsatellites. For the first challenge, we propose a framework jointly uti-lizing colour, object and scene-level information to predict whetherthe topic of an article containing an image is a flood event or not.Visual features are combined using early and late fusion techniquesachieving an average F1-score of82.63,82.40,81.40and76.77. Forthe multi-modal flood level estimation, we rely on both visualand textual information achieving an average F1-score of58.48and46.03, respectively. Finally, for the flooding detection in time-based satellite image sequences we used a combination of classicalcomputer-vision and machine learning approaches achieving anaverage F1-score of58.82%
Active Learning for Event Detection in Support of Disaster Analysis Applications
Sep 27, 2019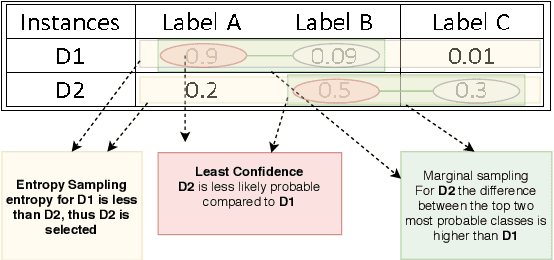
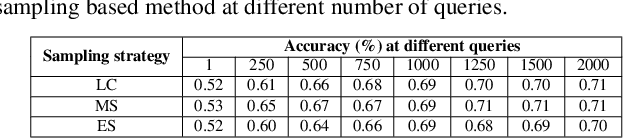
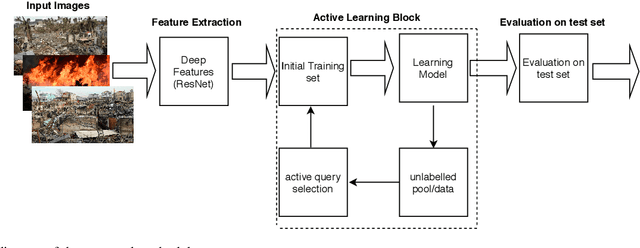
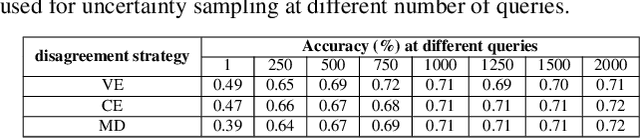
Abstract:Disaster analysis in social media content is one of the interesting research domains having abundance of data. However, there is a lack of labeled data that can be used to train machine learning models for disaster analysis applications. Active learning is one of the possible solutions to such problem. To this aim, in this paper we propose and assess the efficacy of an active learning based framework for disaster analysis using images shared on social media outlets. Specifically, we analyze the performance of different active learning techniques employing several sampling and disagreement strategies. Moreover, we collect a large-scale dataset covering images from eight common types of natural disasters. The experimental results show that the use of active learning techniques for disaster analysis using images results in a performance comparable to that obtained using human annotated images, and could be used in frameworks for disaster analysis in images without tedious job of manual annotation.
Black-box Adversarial ML Attack on Modulation Classification
Aug 01, 2019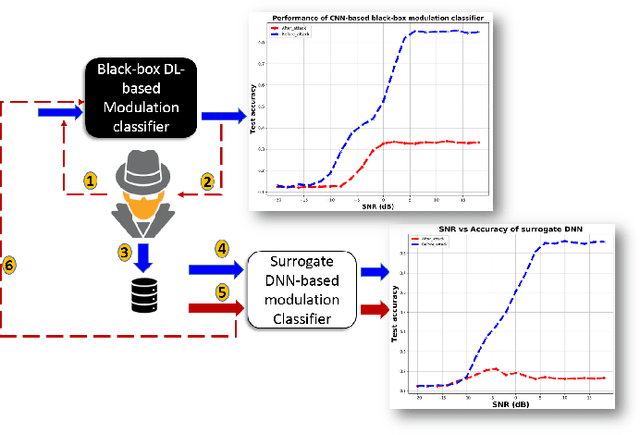
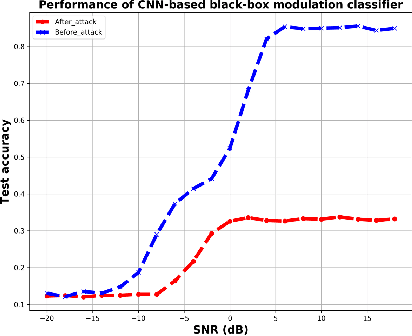
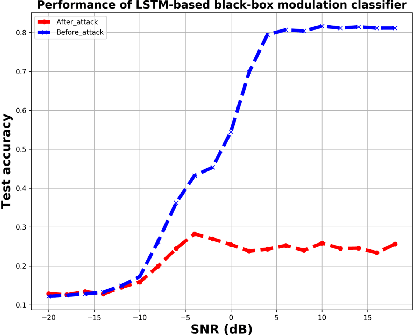
Abstract:Recently, many deep neural networks (DNN) based modulation classification schemes have been proposed in the literature. We have evaluated the robustness of two famous such modulation classifiers (based on the techniques of convolutional neural networks and long short term memory) against adversarial machine learning attacks in black-box settings. We have used Carlini \& Wagner (C-W) attack for performing the adversarial attack. To the best of our knowledge, the robustness of these modulation classifiers has not been evaluated through C-W attack before. Our results clearly indicate that state-of-art deep machine learning-based modulation classifiers are not robust against adversarial attacks.
The Adversarial Machine Learning Conundrum: Can The Insecurity of ML Become The Achilles' Heel of Cognitive Networks?
Jun 03, 2019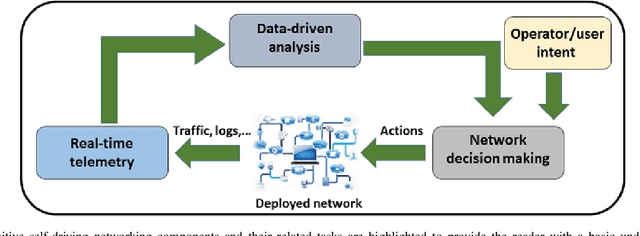
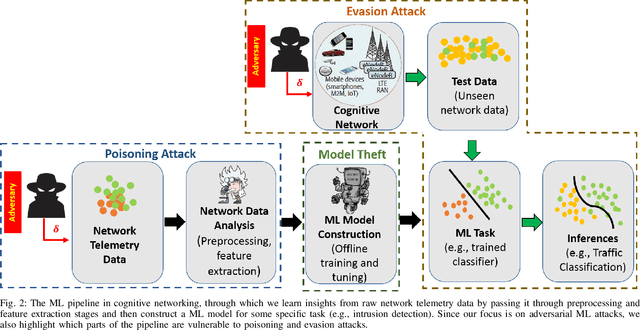
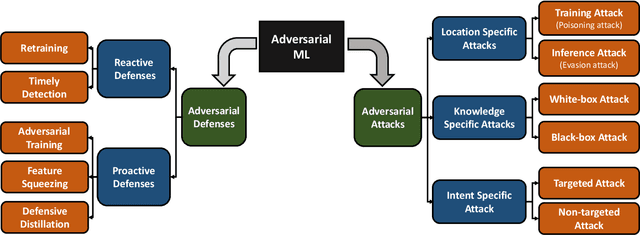
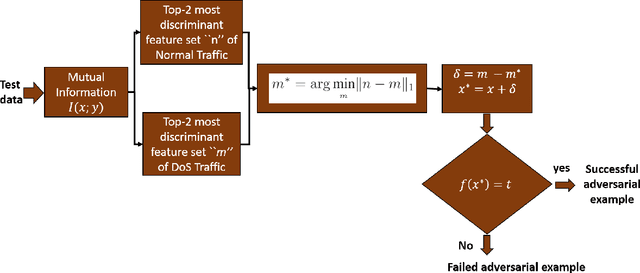
Abstract:The holy grail of networking is to create \textit{cognitive networks} that organize, manage, and drive themselves. Such a vision now seems attainable thanks in large part to the progress in the field of machine learning (ML), which has now already disrupted a number of industries and revolutionized practically all fields of research. But are the ML models foolproof and robust to security attacks to be in charge of managing the network? Unfortunately, many modern ML models are easily misled by simple and easily-crafted adversarial perturbations, which does not bode well for the future of ML-based cognitive networks unless ML vulnerabilities for the cognitive networking environment are identified, addressed, and fixed. The purpose of this article is to highlight the problem of insecure ML and to sensitize the readers to the danger of adversarial ML by showing how an easily-crafted adversarial ML example can compromise the operations of the cognitive self-driving network. In this paper, we demonstrate adversarial attacks on two simple yet representative cognitive networking applications (namely, intrusion detection and network traffic classification). We also provide some guidelines to design secure ML models for cognitive networks that are robust to adversarial attacks on the ML pipeline of cognitive networks.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge