Hanna Bogucka
Mitigating Evasion Attacks in Fog Computing Resource Provisioning Through Proactive Hardening
Mar 26, 2026Abstract:This paper investigates the susceptibility to model integrity attacks that overload virtual machines assigned by the k-means algorithm used for resource provisioning in fog networks. The considered k-means algorithm runs two phases iteratively: offline clustering to form clusters of requested workload and online classification of new incoming requests into offline-created clusters. First, we consider an evasion attack against the classifier in the online phase. A threat actor launches an exploratory attack using query-based reverse engineering to discover the Machine Learning (ML) model (the clustering scheme). Then, a passive causative (evasion) attack is triggered in the offline phase. To defend the model, we suggest a proactive method using adversarial training to introduce attack robustness into the classifier. Our results show that our mitigation technique effectively maintains the stability of the resource provisioning system against attacks.
Energy Savings by Task Offloading to a Fog Considering Radio Front-End Characteristics
Apr 26, 2021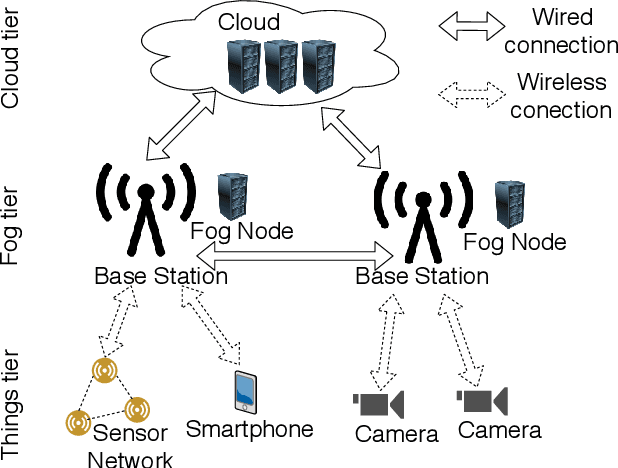
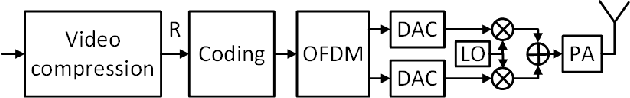
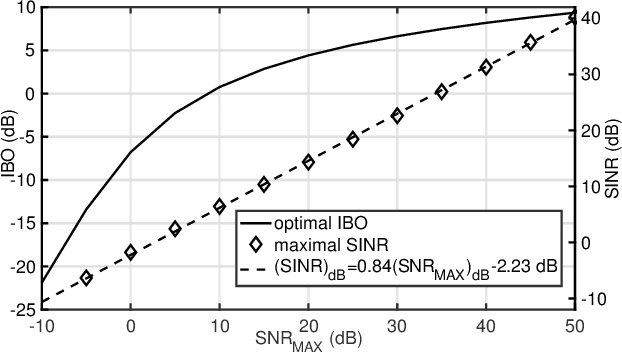
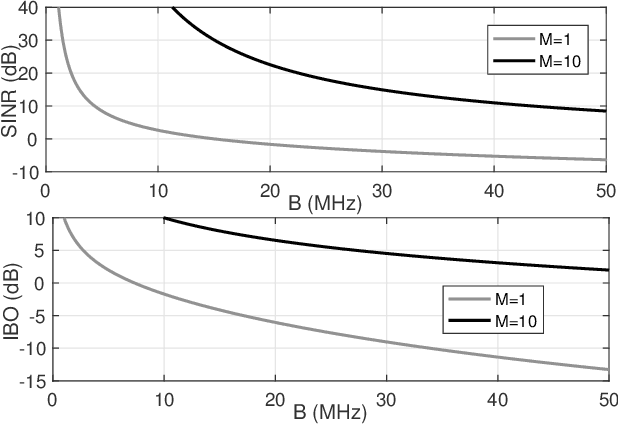
Abstract:Fog computing can be used to offload computationally intensive tasks from battery powered Internet of Things (IoT) devices. Although it reduces energy required for computations in an IoT device, it uses energy for communications with the fog. This paper analyzes when usage of fog computing is more energy efficient than local computing. Detailed energy consumption models are built in both scenarios with the focus set on the relation between energy consumption and distortion introduced by a Power Amplifier (PA). Numerical results show that task offloading to a fog is the most energy efficient for short, wideband links.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge