Amey Kasar
Benchmarking and Comparing Popular Visual SLAM Algorithms
Dec 21, 2018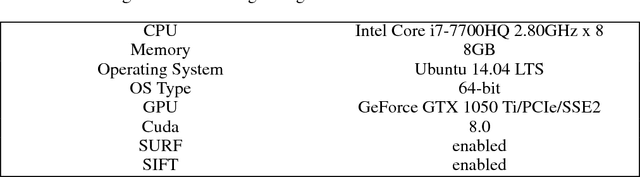
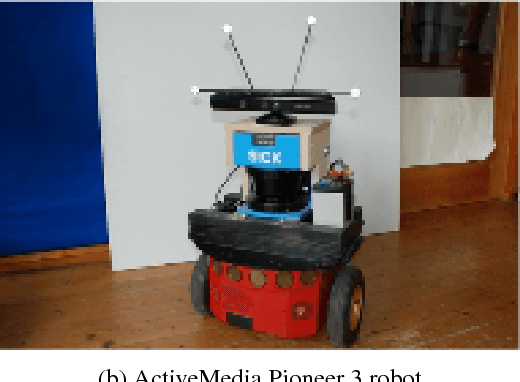
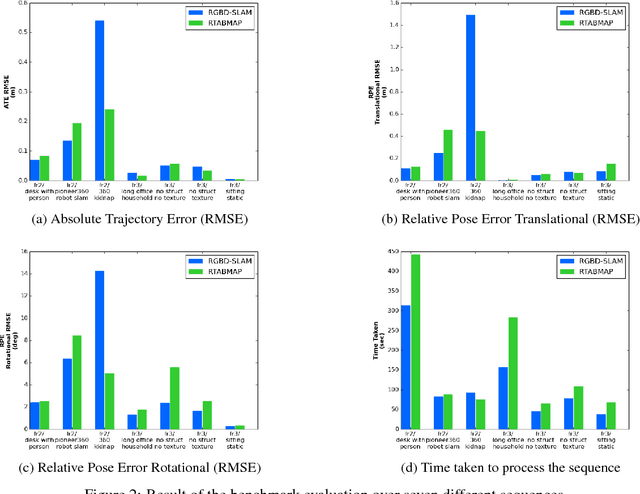

Abstract:This paper contains the performance analysis and benchmarking of two popular visual SLAM Algorithms: RGBD-SLAM and RTABMap. The dataset used for the analysis is the TUM RGBD Dataset from the Computer Vision Group at TUM. The dataset selected has a large set of image sequences from a Microsoft Kinect RGB-D sensor with highly accurate and time-synchronized ground truth poses from a motion capture system. The test sequences selected depict a variety of problems and camera motions faced by Simultaneous Localization and Mapping (SLAM) algorithms for the purpose of testing the robustness of the algorithms in different situations. The evaluation metrics used for the comparison are Absolute Trajectory Error (ATE) and Relative Pose Error (RPE). The analysis involves comparing the Root Mean Square Error (RMSE) of the two metrics and the processing time for each algorithm. This paper serves as an important aid in the selection of SLAM algorithm for different scenes and camera motions. The analysis helps to realize the limitations of both SLAM methods. This paper also points out some underlying flaws in the used evaluation metrics.
Towards Decentralization of Social Media
Nov 28, 2018
Abstract:Facebook uses Artificial Intelligence for targeting users with advertisements based on the events in which they engage like sharing, liking, making comments, posts by a friend, a group creation, etcetera. Each user interacts with these events in different ways, thus receiving different recommendations curated by Facebook's intelligent systems. Facebook segregates its users into chambers, fragmenting them into communities. The technology has completely changed the marketing domain. It is however caught in a race for our finite attention with a motive to make more and more money. Facebook is not a neutral product. It is programmed to get users addicted to it with a goal of gaining added information about the users and optimizing the recommendations provided to the users according to his or her preferences. This paper delineates how Facebook's recommendation system works and presents three methods to safeguard human vulnerabilities exploited by Facebook and other corporations.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge