Ali Abdullah S. AlQahtani
Zero-Effort Two-Factor Authentication Using Wi-Fi Radio Wave Transmission and Machine Learning
Mar 04, 2023Abstract:The proliferation of sensitive information being stored online highlights the pressing need for secure and efficient user authentication methods. To address this issue, this paper presents a novel zero-effort two-factor authentication (2FA) approach that combines the unique characteristics of a users environment and Machine Learning (ML) to confirm their identity. Our proposed approach utilizes Wi-Fi radio wave transmission and ML algorithms to analyze beacon frame characteristics and Received Signal Strength Indicator (RSSI) values from Wi-Fi access points to determine the users location. The aim is to provide a secure and efficient method of authentication without the need for additional hardware or software. A prototype was developed using Raspberry Pi devices and experiments were conducted to demonstrate the effectiveness and practicality of the proposed approach. Results showed that the proposed system can significantly enhance the security of sensitive information in various industries such as finance, healthcare, and retail. This study sheds light on the potential of Wi-Fi radio waves and RSSI values as a means of user authentication and the power of ML to identify patterns in wireless signals for security purposes. The proposed system holds great promise in revolutionizing the field of 2FA and user authentication, offering a new era of secure and seamless access to sensitive information.
Technical Report-IoT Devices Proximity Authentication In Ad Hoc Network Environment
Oct 01, 2022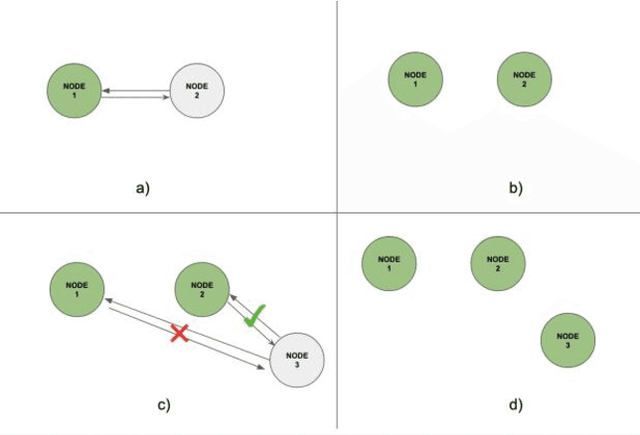
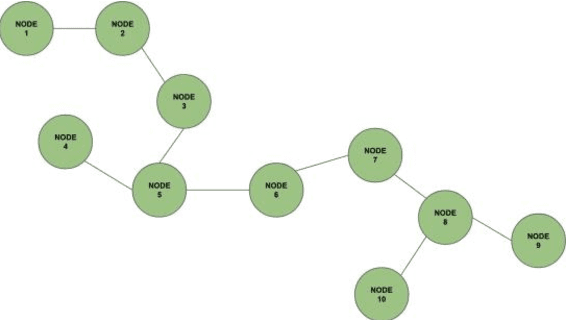
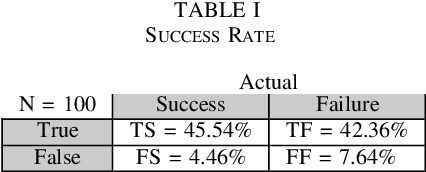
Abstract:Internet of Things (IoT) is a distributed communication technology system that offers the possibility for physical devices (e.g. vehicles home appliances sensors actuators etc.) known as Things to connect and exchange data more importantly without human interaction. Since IoT plays a significant role in our daily lives we must secure the IoT environment to work effectively. Among the various security requirements authentication to the IoT devices is essential as it is the first step in preventing any negative impact of possible attackers. Using the current IEEE 802.11 infrastructure this paper implements an IoT devices authentication scheme based on something that is in the IoT devices environment (i.e. ambient access points). Data from the broadcast messages (i.e. beacon frame characteristics) are utilized to implement the authentication factor that confirms proximity between two devices in an ad hoc IoT network.
 Add to Chrome
Add to Chrome Add to Firefox
Add to Firefox Add to Edge
Add to Edge